Endpoint Protection Services
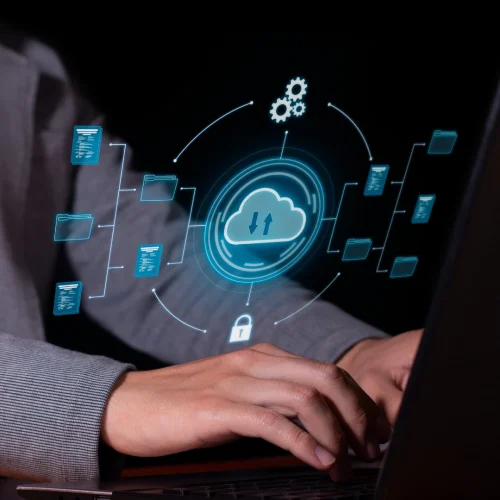
The threat of a Cyber attack to your business exists every moment. We offer endpoint protection services that will help you keep your data, devices, and even operations safe with trustful security controls. Do not wait until the situation goes out of hand; do protect your business now.
To Assist Your Business Use Only Reliable Endpoint Security Solutions
The risk of cyber-attacks does not depend on business hours, therefore endangering devices, information, and even processes. Endpoint Protection allows for continuous surveillance, fast threat response, and slows down threat resolution to ensure that no breach happens in the business operations. Defend your significant resources and stay free from stress.
Safeguard Your Organization against Cybersecurity Risks
Your organization is under constant threat from malware, ransomware, and cyber attacks. With Endpoint Protection, there is round the clock monitoring, advanced threat management techniques and quick counter measures to ensure the protection of your devices and data. Have confidence that your business remains protected and able to withstand threats regardless of their sophistication.

Complete Security for Your Devices and Data
Safeguard your company from cyber attack with endpoint protection services that eliminate threats even before they materialize.
Complete backup solutions for your devices and information without compromise.
Intelligent Threat Detection
- Feature: Threat detection in real-time
- Benefit: Offers protection from viruses, ransomware and other forms of cyber-crimes.
Continuous Supervision
- Feature: 24/7-Every-Day-Daily Endpoint Monitoring
- Benefit: Threats are monitored and responded to at all times.
Responding to Incidents in a Timely Manner
- Feature: Threat Containment in a Drawn-Out Manner
- Benefit: Contains security breaches and makes it possible to perform business operations in a quite short time, in a normal way.
Encryption of Endpoints
- Feature: Data Encrypt
- Benefit: Protects confidential data from unauthorized usage while stopping third parties from accessing the data.
Management of Patches
- Feature: Patch Management Solution
- Benefit: Updates systems with new patches therefore minimizing the windows of vulnerabilities.
Advanced Training on End-Users’ Security
- Feature: Security Communique
- Benefit: Diminishes chances of human error and improves security level in the organization.
Advantages
Reinforced protection
Use superior measures to defend your gadgets as well as the information contained in them from any threats.
Operational Effectiveness
Enhance endpoint security administration and lessen the occurrence of idle time.
Preemptive Measures
Detect and counteract potential threats long before they affect your organization.
Confidentiality
Protect all yak sensitive data from unauthorized breach.
Professional Support
Take advantage of our in-house security experts.
Continuous Monitoring
Ensure ongoing protection with 24/7 endpoint monitoring.
Functionality
Real-time Crime Prevention
Defenses against viruses, trojans, hacking and similar threats.
End-Point Supervision On Round-The-Clock Basis
Watches closely and takes action on threats at once.
Threat Containment within the Shutter’s Open Window
Decreases the extent of damages that come with breaches in security.
End-To-End Data Encryption
Provides protection for sensitive data and restricts access to it to only the designated users.
Automated Patch Deployment
Helps ensure that all the endpoints are protected from current threats.
Security Awareness Training
Improves the knowledge of the personnel on the most effective measures of endpoint security.
Frequently Asked Questions
Endpoint Protection is a broad term describing security packages that focus on safeguarding branches from cyber threat - such branches are computers, mobile devices.
It is based on the amalgamation of hardware and software solutions which focus on monitoring, detecting, and eliminating by responding possible threat on endpoints.
It helps in protecting private information, preventing unwarranted entry, and lessening the possible occurrence of information hacking.
For instance antivirus software protects from virus, worm, trojan, spyware, adware and other forms of threats.
Yes, Most of the Endpoint Protection pests incorporate a bough-millet centralized management for monitoring and controlling the operations remotely.
In order to always be protected from new threats, regular updates are imperative, and we recommend such changes to be made once every quarter.
The Company offers, in addition to assessments, periodic support and consultations aimed at the improvement of the client’s cybersecurity level.
Quarantine the endpoint that is at risk and then call your Endpoint Protection Provider for assistance.
Oh yes! Endpoint protection services are flexible and can be designed for all ranges of companies.
In order to always be protected from new threats, regular updates are imperative, and we recommend such changes to be made once every quarter.
Start Securing Your Endpoints
With Smart Growth Solutions Endpoint Protection Services Today.